Massive Data Breach at Caracal Corporation Exposes Millions
🚨 Major Data Breach! Caracal Corporation's sensitive customer data leaked, affecting millions. Full names, addresses, and banking info exposed. Stay vigilant! #DataBreach #CyberSecurity
Caracal Corporation is a leading supplier company known for its extensive network and quality products. As of 2024, the company serves millions of customers worldwide, providing a variety of products and services that cater to both individual and corporate needs.
Breach Details
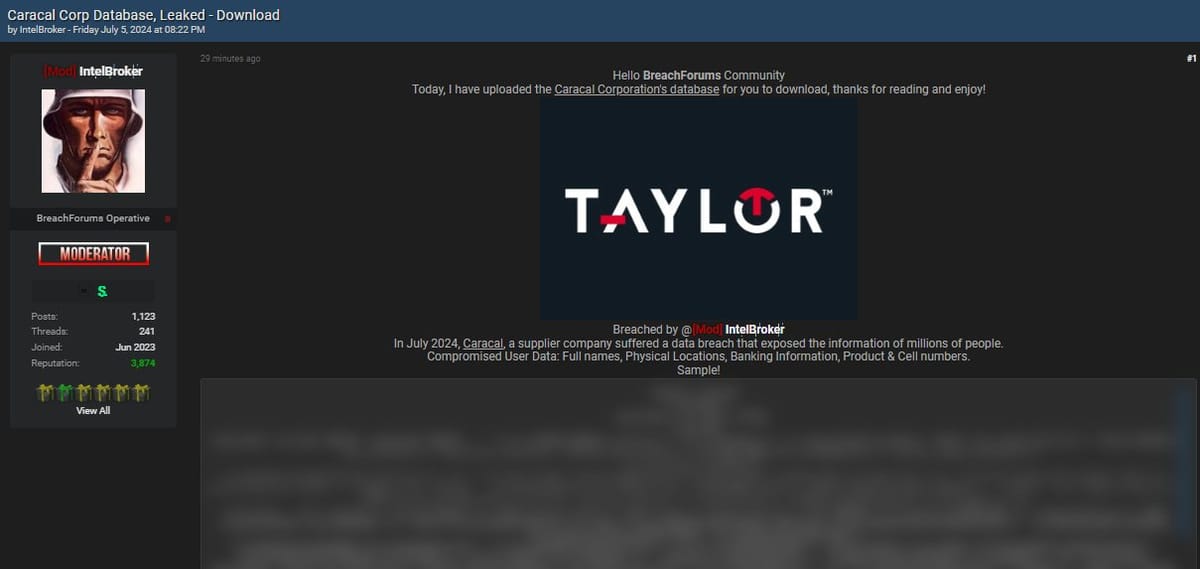
In July 2024, Caracal Corporation experienced a significant data breach. The incident was disclosed on BreachForums by a user named IntelBroker, a known entity in the cybercrime community. This breach exposed sensitive information of millions of users.
Compromised Data Includes:
- Full names
- Physical addresses
- Banking information
- Product details
- Cell phone numbers
The breach was significant due to the volume and sensitivity of the data exposed. The leaked database was made available for download on the dark web, exacerbating the potential for misuse.
Threat Actor Profile: IntelBroker
Overview
IntelBroker is a notorious threat actor known for orchestrating a series of high-profile data breaches across various industries and government entities. Active on underground forums like BreachForums, IntelBroker has a reputation for selling access to compromised systems and data, often targeting large organizations and critical infrastructure.
Notable Activities
IntelBroker has claimed responsibility for breaches involving major corporations such as Apple, AMD, Zscaler, General Electric, AT&T, and Home Depot, as well as government agencies including Europol, the U.S. Department of Transportation, and the Pentagon (Malpedia) (SOCRadar® Cyber Intelligence Inc.). These breaches have involved the exfiltration of sensitive information, such as source code, classified documents, and personal data.
Methods and Techniques
IntelBroker's attack methods are sophisticated and multifaceted, often involving:
- Credential Dumping: Harvesting and using compromised credentials to gain further access within networks.
- Lateral Movement: Moving across networks using valid accounts to explore and compromise additional systems.
- Data Exfiltration: Extracting valuable information via command and control channels (SOCRadar® Cyber Intelligence Inc.).
IntelBroker has also developed ransomware strains, such as the Endurance Ransomware, though its primary focus appears to be on extortion and data leaks rather than ransomware deployment (SOCRadar® Cyber Intelligence Inc.).