📚 Company Overview
Airport School Calicut International Airport is an educational institution located in Calicut, India. The school primarily serves employees of the airport authority, providing educational services to their families. The institution's website is airportschool.ac.in.
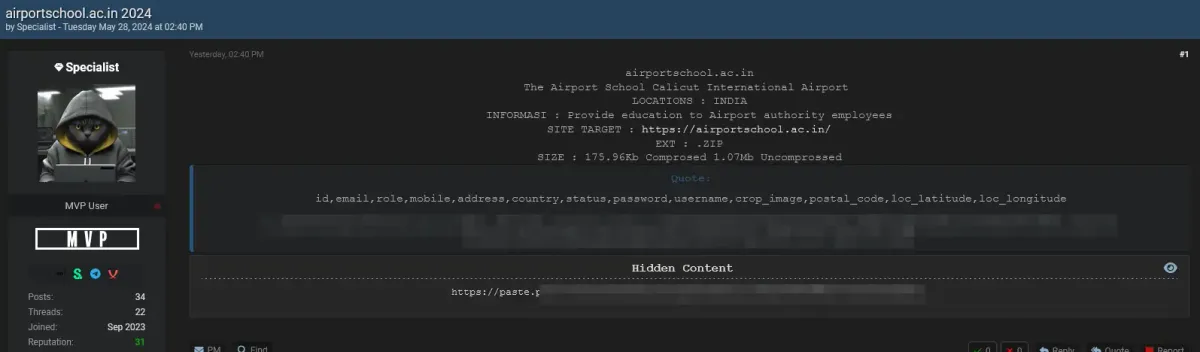
🚨 Breach Details
- Date of Breach: May 28, 2024
- Disclosed by: Specialist (Forum User)
- Data Compromised:
- ID
- Role
- Mobile Number
- Address
- Country
- Status
- Password
- Username
- Profile Image
- Postal Code
- Location Coordinates (Latitude and Longitude)
- Size of Data: 175.96 KB (compressed), 1.07 MB (uncompressed)
- Format: .zip file
The breach was announced on a forum by a user named "Specialist," who provided a link to the compromised data hosted on a paste site. The post included detailed information about the type of data compromised.
👥 Threat Actor Profile: Specialist
Alias: Specialist
Activities: Specialist is an active user on several hacking forums known for disclosing data breaches. This individual is associated with the recent data breach at the Airport School Calicut International Airport and has previously been involved in various other incidents.
Modus Operandi: Specialist typically posts detailed information about the data breaches, including the type of data compromised and sometimes links to download the data. This behavior is indicative of a pattern seen among hackers who seek recognition within their community by showcasing their exploits.
Notable Breaches Linked to Specialist
- Cutout.Pro Breach
- Date: February 2024
- Details: Specialist, under the alias "KryptonZambie," disclosed a breach involving 20 million users of Cutout.Pro, an AI-powered visual design platform. The compromised data included email addresses, hashed and salted passwords, IP addresses, and other personal information (TechRadar) (RedPacket Security).
- Pixlr Breach
- Date: January 2021
- Details: Specialist, using the alias "ShinyHunters," leaked 1.9 million user records from Pixlr, an online photo editing application. The data exposed included email addresses, login names, hashed passwords, and other sensitive information (BleepingComputer) (ITPro).
Impact and Recommendations
The activities of Specialist highlight the vulnerabilities in both large and small organizations. The breaches often result in significant data exposure, leading to privacy risks and potential financial losses for the affected users and organizations.
Recommendations:
- Monitor for Unusual Activity: Affected users should monitor their online accounts for any suspicious activity and immediately change passwords if a breach is suspected.
- Implement Strong Security Measures: Organizations should enforce strong password policies, use multi-factor authentication, and regularly update their security protocols.
- Educate Users: Continuous education on recognizing phishing attempts and other cyber threats is crucial for minimizing risks.
By understanding the tactics and patterns of threat actors like Specialist, organizations can better prepare and defend against potential data breaches.
For further details and updates on cybersecurity threats, you can follow reliable sources such as TechRadar, RedPacket Security, and BleepingComputer (TechRadar) (RedPacket Security) (BleepingComputer).
💥 Impact Analysis
The breach of Airport School's data can have significant implications:
- Personal Impact: Exposure of personal information, including contact details and location, poses risks of identity theft and privacy violations for affected individuals.
- Organizational Impact: Potential reputational damage to the Airport School and loss of trust from employees and stakeholders.
- Security Impact: Compromised passwords and usernames may lead to unauthorized access to personal and institutional accounts.